Introduction
As enterprises increasingly embrace cloud transformation, the well-architected integration of multiple cloud platforms into the technology infrastructure becomes more and more important.
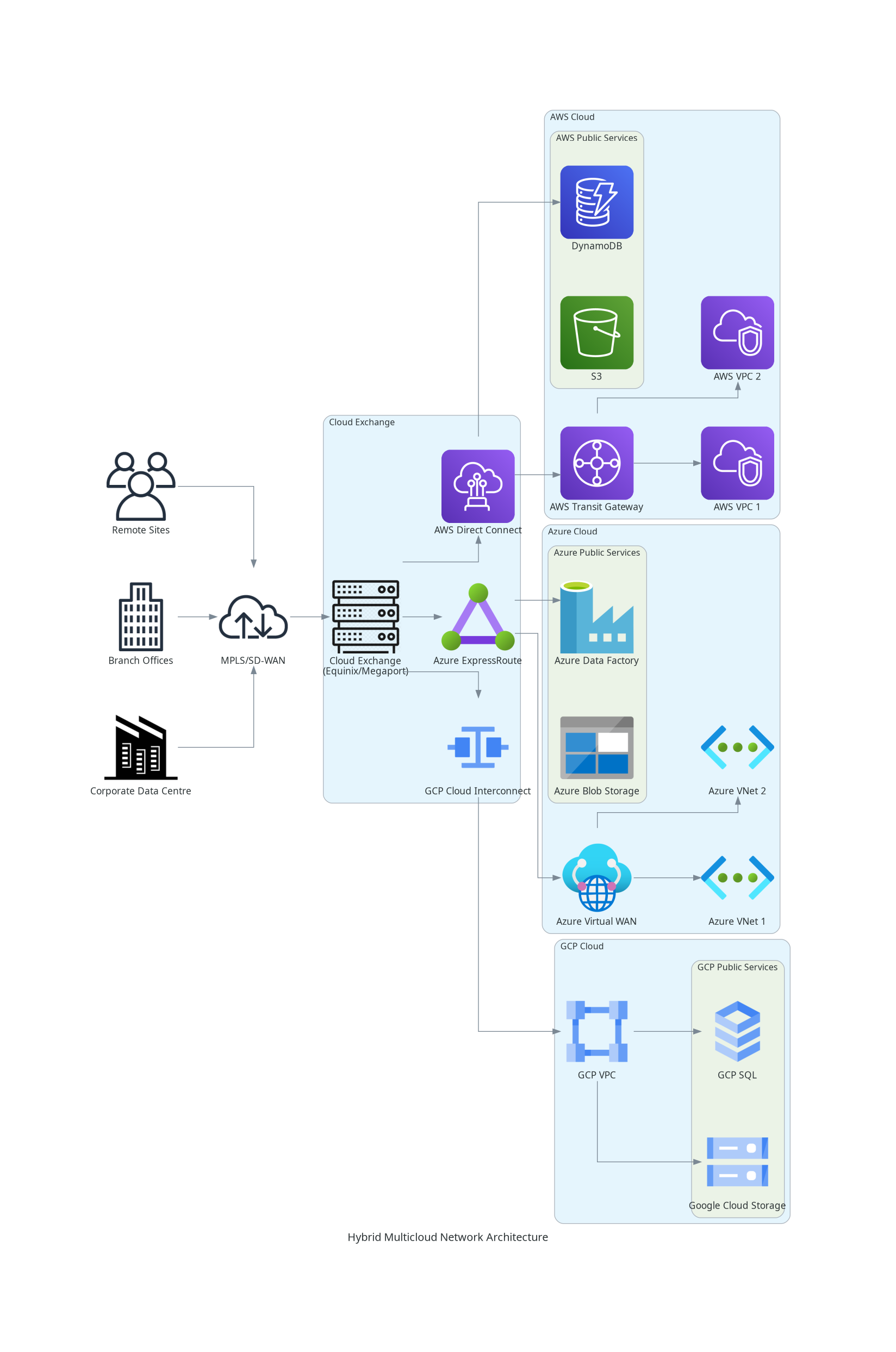
The challenge lies in creating a hybrid multi-cloud network – a network consisting of on-premises infrastructure as well as not just one but multiple hyperscale cloud environments – that ensures seamless connectivity, security, and performance without unnecessary complexity.
Here, we walk through the architecture for a hypothetical global enterprise, connecting AWS, Azure, and GCP to on-premises data centres, branch offices, remote employees, and third-party partners in a cohesive and efficient manner.
Establishing a Strong Cloud Foundation
At the core of our network, we have virtual private environments within AWS, Azure, and GCP, each hosting critical workloads.
The AWS environment contains a Virtual Private Cloud (VPC) with EC2 compute instances, DynamoDB database services, and S3 for object storage.
With Azure we have Virtual Networks (Vnets) containing Virtual Machines (VMs), the Blob Storage service for object storage, and Data Factory for data transformation.
In the Google Cloud tenancy, VPCs house high-performance computing on Google Compute Engine. We also have the SQL service for databases, and Cloud Storage for object storage.
To ensure seamless communication between these environments and the on-prem estate, we implement private, high-bandwidth connectivity using AWS Direct Connect, Azure ExpressRoute, and Google Cloud Interconnect.
These services provide dedicated, low-latency connections between our cloud workloads and corporate sites, eliminating reliance on the public internet.
Connecting the Clouds to On-Premises Infrastructure
Our corporate data centres house legacy applications and high-performance databases that must interact with the cloud workloads efficiently.
To achieve this, we establish connections between the cloud environments and the on-prem network through Equinix Fabric, enabling private, high-speed connection to AWS, Azure, and GCP.
To facilitate traffic routing within each tenancy, we deploy AWS Transit Gateway for interconnecting VPCs across multiple AWS accounts, and Azure Virtual WAN for secure, optimised connectivity across regional Azure VNets.
These services simplify the management of otherwise complex interconnections.
Enabling Branch Office and Remote Workforce Connectivity
With a global workforce spread across multiple office locations and remote setups, we implement a flexible yet secure approach to connectivity.
Instead of relying solely on traditional MPLS circuits, we deploy Cisco SD-WAN to intelligently route traffic between branch offices, cloud resources, and data centres.
This allows us to optimise performance dynamically, reducing latency and improving application responsiveness.
For remote workers, we implement Zero Trust Network Access (ZTNA) principles, ensuring that users securely access applications without exposing internal networks.
Managing Third-Party and Partner Access
Various external vendors and partners require controlled access between specific workloads in their cloud tenancies and ours, without compromising security.
Instead of exposing services over the internet, we use AWS PrivateLink, Azure Private Link, and Google Cloud Private Service Connect to allow private, restricted access.
Okta and Microsoft Entra ID provide federated identity management, ensuring third parties authenticate through their own identity providers and thus minimise administrative overhead.
Security and Compliance at Every Layer
Security is embedded throughout this architecture, with Secure Services Edge (SSE) services like Firewall-as-a-Service (FaaS), Cloud Access Security Broker (CASB) and Secure Web Gateway (SWG) combining with the SDWAN connectivity to form a comprehensive Secure Access Services Edge (SASE) platform.
This is complemented by cloud-native security monitoring solutions, with AWS Security Hub, Microsoft Defender for Cloud, and Google Security Command Center provide real-time visibility into the security posture within the cloud environments.
Continuous Monitoring and Cost Optimisation
With such a complex network spanning multiple cloud providers and locations, proactive monitoring and cost management are critical.
AWS CloudWatch, Azure Monitor, and Google Cloud Operations Suite provide real-time insights, helping to detect potential issues before they impact performance.
For network analytics, we rely on Cisco ThousandEyes to gain visibility into network performance across the hybrid multicloud environment.
Cost management tools, such as AWS Cost Explorer, Azure Cost Management and GCP Billing Reports, allow us to continuously optimise resource usage.
Conclusion
The elements described and illustrated constitute a basic constellation of services, for the sake of clarity and simplicity. A typical hybrid multicloud estate would comprise a larger and more complex mix of cloud services.
There are also options available to interconnect the different cloud environments directly without first going through the SDWAN network. However while this may represent a more efficient approach in certain instances, there are good reasons to keep the on-prem network as the pivot in the architecture. Primary among these is so that the bulk of the connectivity remains centralised in the SDWAN and as such be more maintainable, and robust against future changes in the cloud vendor product landscape.
To sum up, building an efficient hybrid multicloud network requires more than just connecting disparate services—it demands a cohesive, well-architected approach that balances performance, security, and scalability. We achieve this by leveraging SASE features, end-to-end security and monitoring products and remote and third-party private connectivity services.
Leave a Reply